Thorough remediation most attempts to remove malware focus primarily on the active executable but leave numerous components littered throughout the system making the system highly vulnerable to re infection.
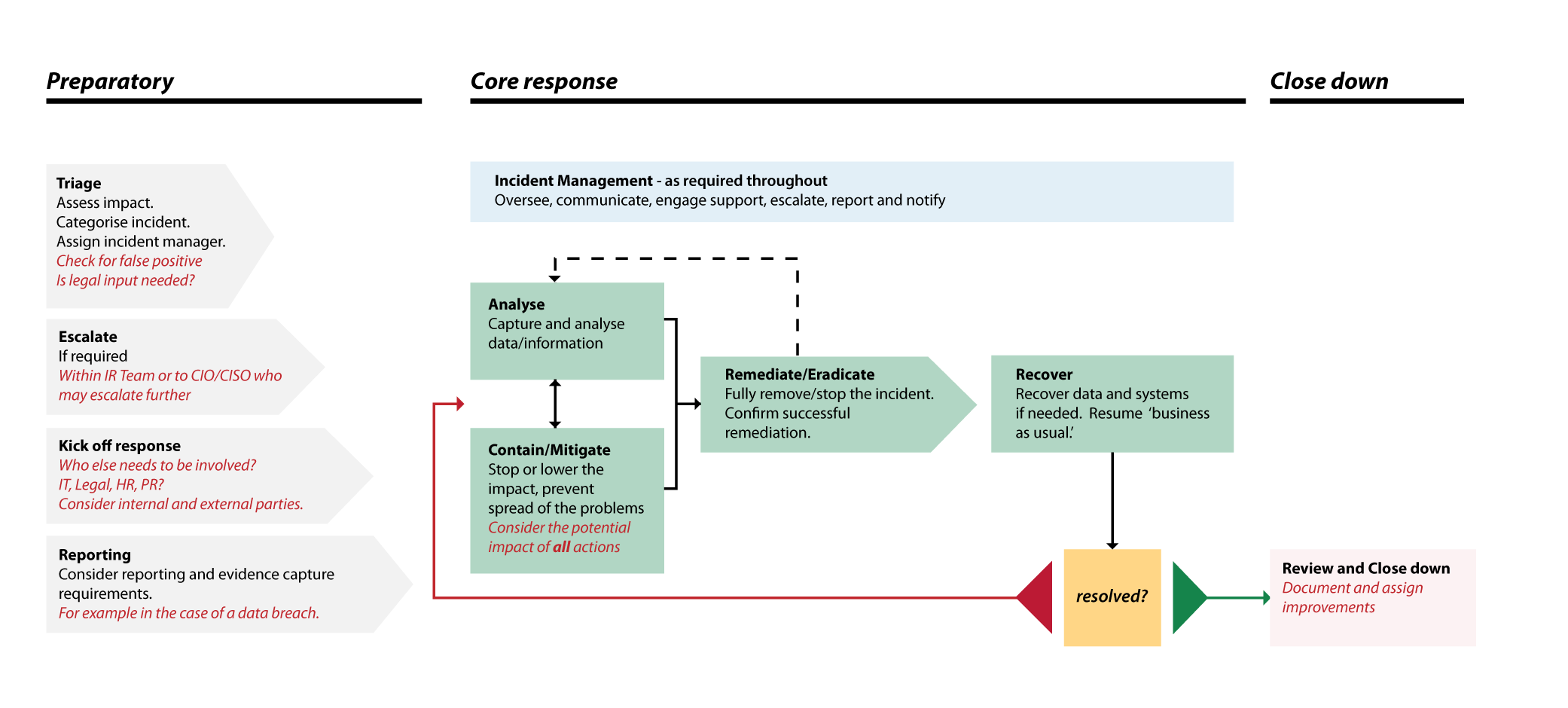
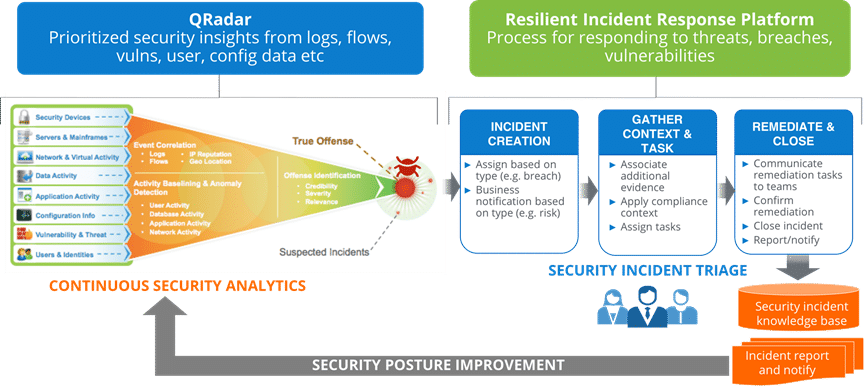
Malware incident response process flow.
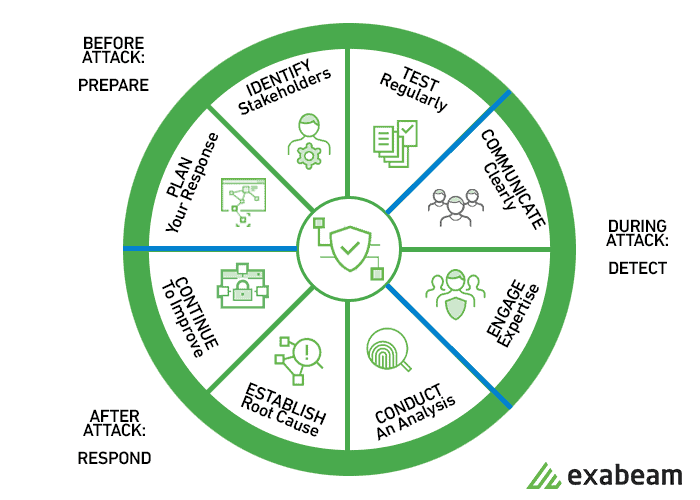
Automating threat response helps businesses accelerate their incident response workflows while reducing malware dwell times.
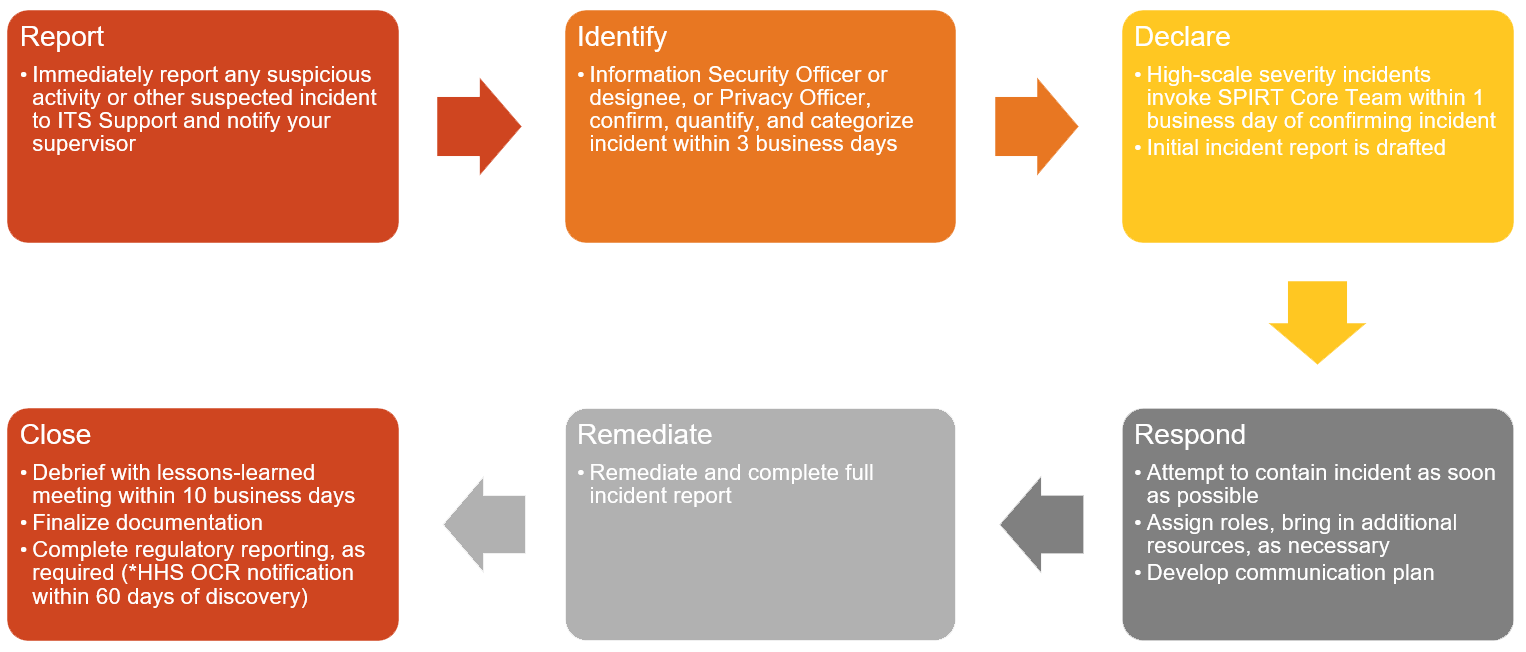
An incident response plan is a documented written plan with 6 distinct phases that helps it professionals and staff recognize and deal with a cybersecurity incident like a data breach or cyber attack.
Learn how to manage a data breach with the 6 phases in the incident response plan.
Malware incident response steps on windows and determining if the threat is truly gone.
Incident response helps organizations ensure that organizations know of security incidents and that they can act quickly to minimize damage caused.
Once malware has been removed and the system s have been brought back to production a post incident analysis is needed in order to identify the causes of the infection and the defenses that need.
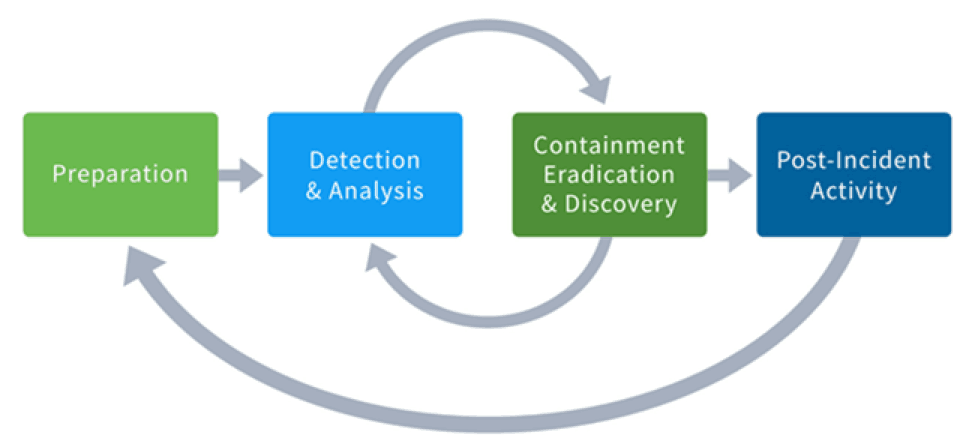
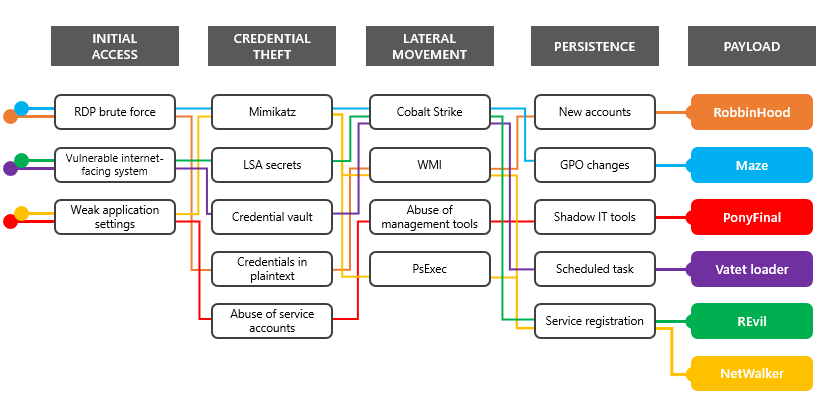
Responding to and recovering from malware is a complex process that requires significant preparation.
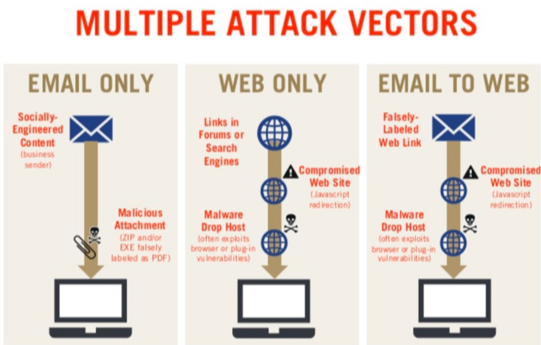
The growing threat of malware infections.
An incident response process is the entire lifecycle and feedback loop of an incident investigation while incident response procedures are the specific tactics you and your team will be involved in during an incident response process.
The aim is also to prevent follow on attacks or related incidents from taking place in the future.
A malware incident response plan is not one that should focus on an active attack.
Malware apts and other threats are getting smarter but so are endpoint detection and response products.
Instead it needs to concentrate on the payload left.
Share malware can be a sneaky little beast.
When dealing with malware it is extremely important to not only.
What is an incident response plan for cyber security.
The 6 steps in depth.
Computer and network tool kits to add remove components wire network cables.
Malware response plan recovers data in 6 steps.
Once it s on your computer or network it may be hard to detect unless you re explicitly looking for it.
For this case we ll walk through a typical remote access trojan based incident.
The sans ir process focuses on a typical malware based event focused on a single threaded incident and response.